Matter-Level Access Control: Scaling AI Confidentiality to the Entire Firm
Why Access Control Has to Be Built In, Not Bolted On
A firm with hundreds of attorneys across dozens of practice groups cannot treat access control as an afterthought. When AI tools extract tasks from emails, summarize threads, and build contact intelligence, the question of who can see that output becomes as important as the output itself.
Matters have defined teams. Those teams change. And some attorneys must be kept away from certain matters entirely. Access control needs to reflect that structure — not offer broad organizational access or leave administrators to manage permissions manually.
Clevermore is built around this reality from the ground up. Every piece of AI-generated content is scoped to a specific matter and a specific set of authorized users — not as a configuration option, but as a core architectural constraint.
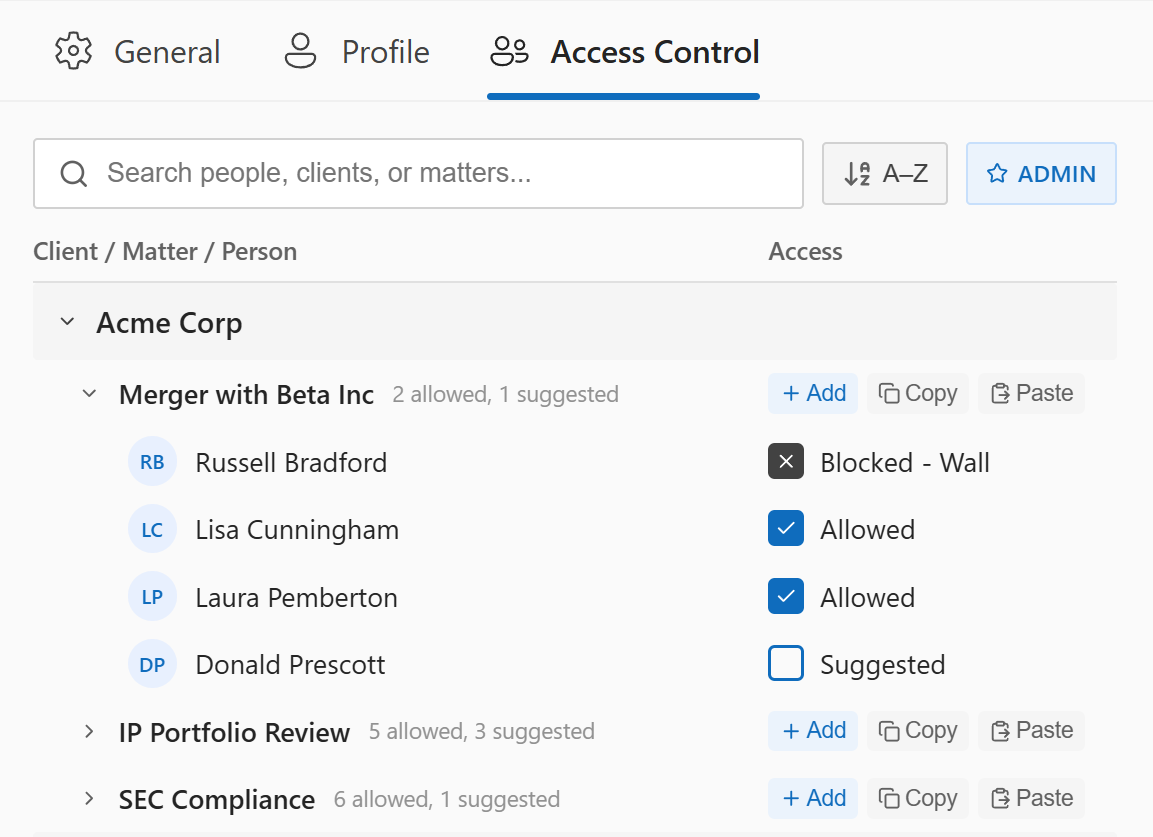
Per-matter access lists in the Clevermore Outlook add-in
Per-Matter Access Lists
In Clevermore, every client matter maintains its own list of authorized users. Content tied to a matter — extracted tasks, email summaries, wiki entries, contact intelligence — is only visible to users on that matter's access list. If you're not on the list, the data doesn't exist as far as your account is concerned.
This is the inclusionary model: rather than trying to define every person who shouldn't see something, you define who should. It's a tighter boundary by default, and it maps naturally to how law firms already think about staffing. It also directly addresses the duty of secrecy — AI-generated content from a privileged thread cannot leak to an unauthorized user because the data literally does not exist in their partition.
- Matter-scoped visibility — All AI-generated content inherits the access permissions of its source matter. An extracted task from a privileged email thread is visible only to users authorized on that matter.
- Database-level enforcement — Access control isn't a UI filter that can be circumvented. It's enforced at the data layer through partition-level isolation, the same architecture described in our privacy-first design.
- No shared knowledge pool — There is no firm-wide AI knowledge base where one matter's insights could surface in another matter's context. Each matter's data is siloed completely.
Email participants are suggested for matter access. Ethical walls override all other permissions.
Intelligent Suggestions From Email Patterns
The hardest part of access control at scale isn't the enforcement — it's the setup. If every matter requires a partner to manually add each authorized user, adoption stalls. Attorneys won't use a tool that creates administrative overhead before it creates value.
Clevermore solves this by analyzing email participation patterns. When emails flow through a matter, the system identifies the participants and builds a suggestion list of users who appear to be actively involved. A partner or administrator can then approve suggested users with a single click — or remove someone who shouldn't have access.
This approach reflects a practical insight: the people who are emailing about a matter are, overwhelmingly, the people who should have access to that matter's AI-generated content. Rather than asking partners to build lists from scratch, the system proposes lists based on actual work patterns and lets partners confirm.
- Email-derived suggestions — Users who appear on matter-related email threads are automatically surfaced as candidates for the access list.
- One-click approval — Partners and administrators can approve or reject suggested users without navigating away from their workflow.
- No implicit access — Appearing on the suggestion list does not grant access. Every addition requires explicit approval from an authorized administrator or partner.
Ethical Wall Integration
Suggestion lists and manual approvals handle the inclusionary side — who should have access. But large firms also need to enforce the exclusionary side: who must be prevented from accessing certain matters, regardless of their role or email involvement.
This is where ethical walls come in. Firms that manage conflicts through systems like Intapp Walls maintain dynamic rules about which attorneys are walled off from which matters or clients. These walls exist to prevent conflicts of interest — a core obligation under the duty of loyalty that Georgetown Law professor Jonah Perlin identifies as the least examined AI confidentiality risk.
Clevermore integrates with ethical wall systems to enforce these restrictions automatically. If an attorney is walled off from a matter, they cannot be added to that matter's access list — not manually, not through suggestion, not through any workflow. The wall is absolute. Cross-client contamination isn't just a theoretical model-training risk — it's a practical risk any time an attorney working on competing matters has access to both clients' AI-processed content. Per-matter isolation, combined with ethical wall enforcement, prevents this structurally rather than relying on attorney judgment alone.
- Automatic enforcement — Ethical wall restrictions are checked at every access decision. Walled attorneys see no data, receive no suggestions, and cannot be granted access.
- Conflict prevention at the data layer — Rather than relying on attorneys to self-police (or on manual compliance checks after the fact), the system prevents conflicts structurally.
- Real-time synchronization — Changes to ethical wall configurations are reflected immediately. When a wall is erected or modified, access lists are updated without manual intervention.
Built for How Firms Actually Work
The firms having the most productive conversations about AI adoption are not asking "is it safe?" in the abstract. They're asking specific questions: who controls access? How are conflicts enforced? What happens when staffing changes mid-matter? Can we integrate this with systems we already use?
Per-matter access lists also reduce the blast radius of a security incident. Even if a single user's session were compromised, the exposure is limited to the matters that user is authorized on — not the entire firm's data. Combined with zero-retention AI processing and single-tenant deployment, every layer of the system reinforces the same principle: confidential data should only be accessible to the people who need it, for only as long as they need it.
Matter-level access control answers these questions with architecture, not policy documents. The access model is tied to the work itself — matters, teams, and ethical walls — so it scales naturally with the firm.
If you're evaluating Clevermore for your firm and want to discuss how access control integrates with your existing ethical wall infrastructure, reach out at security@clevermore.ai.
For the full technical details on our privacy architecture, see our Security page and Privacy Policy.